Single Sign-On (ADR)
SSO for IA and IP
This page describes the process for enabling SSO for ADR. If you'd like to set up SSO for AI Incident Assistant or AI Incident Prevention, contact your BigPanda account team.
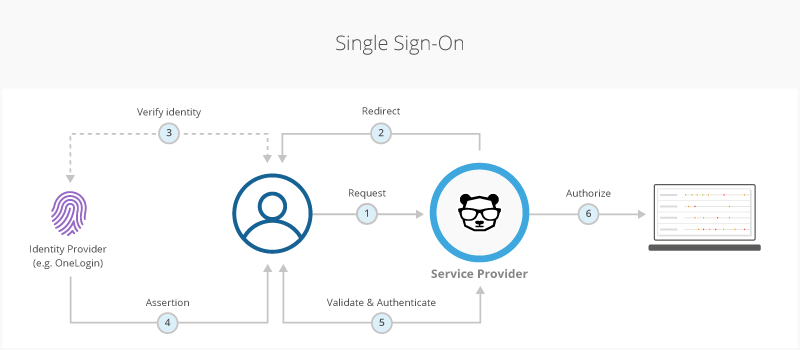
Single Sign-On (SSO) is an authentication process that allows users to log in to multiple systems via a third-party identity provider (IdP).
After an administrator successfully authenticates on the BigPanda website via basic authentication, they can configure their organization to use a SAML 2.0-compliant, third-party IdP for delegated authentication.
When SSO is configured for your organization, all authentication attempts are redirected to the third-party IdP. If a user does not have a valid session with the IdP, they are redirected to a login page where they may be challenged for their username, password, security questions, or multiple factors as determined by the IdP. The IdP then returns the successful identity authorization back to BigPanda, allowing the user to authenticate.
SSO with Just-In-Time (JIT) Provisioning
With BigPanda’s JIT SAML Mapping, SSO provisioning is able to create user accounts automatically based on predefined rules and properties in your SSO provider’s object. See the SSO Configuration documentation for more information.
SSO with BigPanda
Relevant Permissions
Roles with the following permissions can access the Single Sign-On section in BigPanda Settings:
Role Name | Description |
|---|---|
Single Sign-On | View, select, and configure a Single Sign-on provider in BigPanda Settings. |
Permission access levels can be adjusted by selecting either View or Full Access. To learn more about how BigPanda's permissions work, see the Roles Management guide.
Key Features
You can choose to integrate BigPanda with a third-party IdP to take advantage of any security controls and identity management processes that are already established in your organization. The benefits of SSO include:
Added security controls through the IdP, such as enforcing security policies, adding two-factor authentication, or restricting login via a corporate authentication mechanism.
Simplified password management.
Reduced password fatigue and time spent re-entering login details.
Simplified user management, onboarding, and offboarding.
Requirements
Use this information to check whether a specific SAML provider may be able to work with BigPanda, or to troubleshoot implementation problems.
Consideration | BigPanda Functionality |
|---|---|
Supported Federation Protocol | SAML 2.0 |
Supported Encryption Protocol | SHA-256 |
Scope Of User Management | Must be all BigPanda users. BigPanda does not support multiple authentication methods for the same organization. |
Authentication Flow | Supports both SP- and IdP-initiated: - For SP-initiated, with redirect binding from the SP and POST binding from the IdP. - For IdP-initiated, with POST binding from the IdP. |
SAML Request Signature/Assertion Type | Supports only unsigned, unencrypted assertions. |
XML Schema | Follows standards from the SAML 2.0 core specification. |
Username | - Must be an email address. - Must be the same in BigPanda and the IdP. |
Provisioning and De-Provisioning | Manual invitation and deactivation by an administrator from within the BigPanda UI, or via the SCIM Users API . See Invite Users and Manage User Accounts . |
Supported Providers
BigPanda is SAML2 compatible and supports SSO with several third-party IdPs for delegated authentication. Contact BigPanda Support to check whether your provider is supported.
Enable SSO
You may want to enable single sign-on (SSO) to require users to log in to BigPanda via a third-party identity provider (IdP). After SSO is enabled, users must use the SSO provider to log in to BigPanda.
Before you enable SSO, you will need to:
Obtain administrator access to BigPanda.
(Recommended) Inform users that the BigPanda login process is changing.
Email Matching
Your BigPanda email address must match your SSO email.
To enable SSO in BigPanda:
In the top right, click the Settings icon, and then click Single Sign-on.
Select the desired SSO provider.
Follow the on-screen instructions to configure the SSO integration, and then click Validate SSO Config.
A pop-up window will open where you can log in to your SSO provider. Enter your credentials.
If your login is successful, you will be redirected to a new page. Select Activate SSO to enable SSO for your instance. If it fails, you can reconfigure and try again. Contact BigPanda support for assistance, if needed.
Inform all users that they must log in to BigPanda via SSO.
Update SSO details
SSO details, such as certification details cannot be updated independently. To update SSO details, first disable the existing SSO configuration, then reconfigure a new SSO connection with new details.
BigPanda Access During SSO Downtime
If your SSO service is interrupted, users with the Account Administrator role can still access the console using a temporary access link.
To receive a temporary access link in your email, click here and enter the email address associated with your BigPanda account. Once the link is sent to you, you must click it within five minutes or it will time out.
After signing in using the temporary link, you can then assign the admin role to additional users who may need to access BigPanda during the outage. See the Manage Users documentation for more information.
You can also Disable SSO for your entire organization if necessary. However, if you choose to disable SSO, you will need to follow the steps to Enable SSO again with BigPanda once the outage has ended.
Enable SSO Just-In-Time Provisioning
SSO with Just-In-Time (JIT) Provisioning automatically creates user accounts in BigPanda when users first log in via SSO, eliminating the need for manual account creation. Account creation is based on rules and properties defined in your SSO provider’s object.
With JIT SAML mapping, you can also configure roles to automatically sync to BigPanda each time a user logs in.
To enable SSO JIT for your organization, see the SSO Configuration documentation.
Disable SSO
You may want to disable single sign-on (SSO) and require users to log in directly to BigPanda instead. After SSO is disabled, users must reset their passwords to log in to BigPanda.
To disable SSO, you must be signed in with administrator access to BigPanda.
SSO downtime will affect users
Single Sign-On is controlled globally across your organization. Disabling SSO will disable it for all users, not just the admin taking the action.
When SSO is disabled, users who are currently logged in will remain logged in and will not be logged out. Users trying to login while SSO is disabled must use password-based login.
We recommend informing all BigPanda users that the login process will be changing prior to disabling SSO.
To disable SSO for your organization:
In the top right, click the Settings icon and then click Single Sign-on.
Select the SSO provider that is currently configured for BigPanda.
Click Disable SSO.
Click Yes to confirm that you want to disable SSO for your organization.
After following the above steps to disable SSO, the BigPanda configuration can be removed from your SSO provider’s system. We recommend that administrators validate that the new login process works as expected by testing using their own user account.
All BigPanda users will need to switch to the manual login process:
Log out of BigPanda
Log back in using the email address that was tied to your SSO
Follow the instructions to reset your password
Changing SSO Providers
To change SSO providers, follow the steps to Disable SSO. After SSO is disabled, the sign-in screen will switch to BigPanda's basic authentication.
Sign in using a non-SSO BigPanda account that has admin privileges, and then follow the steps to Enable the New SSO Provider.
SSO downtime will affect users
Single Sign-On is controlled globally across your organization. Disabling SSO will disable it for all users, not just the admin taking the action.
When SSO is disabled, users who are currently logged in will remain logged in and will not be logged out. Users trying to login while SSO is disabled must use password-based login.
We recommend informing all BigPanda users that the login process will be changing prior to disabling SSO.
Frequently Asked Questions
FAQ
SSO Protocols
What is the Audience Restriction / Entity ID in production?
What is the ACS used by BigPanda?
BigPanda provides a unique ACS per instance of BigPanda. If you have a Prod and Sandbox instance (or another multi-instance configuration), the ACS will be unique for each one and requires additional steps to enable SSO. Contact Support for assistance.
User Identification
What is the unique identifier in BigPanda for users?
BigPanda defines unique users based on their registered email address. Each email address can only be used in a single instance of BigPanda.
What are the required fields for Users? Can other fields be sent in the SAML assertion?
Email is the only required attribute for a user, but we also suggest including a display name. Email is the primary identifier for users and is also leveraged for Just-In-Time (JIT) provisioning. BigPanda also optionally supports a phone number. Additional fields can be included in the SAML assertion, but they will be ignored by BigPanda.
How will users login to BigPanda with SSO enabled?
Depending on the chosen SSO flow, users will access:
IdP Initiated - After authenticating with their IdP, users select the BigPanda icon in their SSO portal.
SP-Initiated - Users sign in through BigPanda login page a.bigpanda.io/login by entering their username. BigPanda will then authenticate that user against their SSO tool and return the required details to pass the user into the console.
Lifecycle Management
Can SSO exist with other login methods?
When SSO is enabled, users can only access BigPanda through the SSO login.
Does BigPanda require email verification for their account to activate or on first login?
When SSO is enabled, users will get a welcome email sent once configured, but there is no requirement of acknowledgement in order to access BigPanda. On first login, users will be prompted to create a password, but this is asked in the event SSO becomes disabled for any reason in the future.
How are users created in BigPanda?
With SSO enabled, users must be added to the permissioned group within the IdP to be permissioned to BigPanda. With SSO Disabled, users can be added by user profiles with User Management Write privileges.
How are users removed from BigPanda?
With SSO enabled, when a user is removed from the iDP AD group, they will lose their ability to login to BigPanda. In terms of the user deletion, we currently don't support any deletions via SAML. Their user profiles would need to be either manually deleted or updated through our Users API. We also have the concept of a hard deletion which can be executed through our support team.
After authentication, does the solution support automated lifecycle management (auto-provisioning and de-provisioning?)
BigPanda supports provisioning, but does not support automated de-provisioning of user accounts.
General
How do I update my SSO certificate?
To update your SSO certificate, you will need to disable SSO from within the BigPanda UI, and then enable it again using your new certificate. See the Disable SSO and Enable SSO sections for instructions.
Custom Logout URL
If you have a custom logout URL, the BigPanda support team will need to update the certificate manually. Contact BigPanda Support for assistance.
Does BigPanda have a Users API?
BigPanda has a SCIM Users API available.
Does BigPanda support an idle session timeout?
Yes, BigPanda supports an idle session (not maximum) and is configurable on the BigPanda backend. Contact BigPanda Support for assistance.
Is BigPanda a supported application on the Okta Integration Network?
Yes, BigPanda is a supported app. A sample assertion is not available on the network.
Can BigPanda support a custom logout URL?
Yes, contact BigPanda Support for assistance.
Is Multi-Factor Authentication supported?
Multi-factor authentication is not supported at this time.
Next Steps
Find your way around the BigPanda Settings page
Learn about User Management in BigPanda
Learn how to control account access levels with Roles Management